
Introduction
Cybersecurity content marketing for B2B has evolved from a niche marketing function into a strategic enterprise capability. As cyber risk becomes a board-level concern, organizations are expected to communicate security posture, risk mitigation, and trust signals clearly to stakeholders.
In this environment, enterprise organizations cannot rely solely on technical controls. They must also build credible, data-driven narratives that support trust, compliance, and market positioning. That is where a disciplined cybersecurity marketing strategy becomes essential.
Business context and industry background
In large enterprises, cybersecurity communication sits at the intersection of multiple functions. Chief Information Security Officers (CISOs), corporate communications leaders, product marketing teams, and compliance officers all have a stake in how security messaging is developed and distributed.
From what we observe across enterprise environments, cybersecurity content serves several strategic purposes:
- Supporting enterprise sales cycles that often exceed 6–12 months
- Demonstrating regulatory readiness to auditors and partners
- Enabling IT security thought leadership in competitive markets
- Reinforcing investor and board confidence
The demand is accelerating. Gartner has projected that global spending on information security and risk management will surpass $215 billion in 2024, reflecting sustained enterprise prioritization of cyber resilience. As budgets grow, so does the expectation for structured, credible cybersecurity reporting content that aligns with enterprise governance frameworks.
For large SaaS providers, cloud platforms, and regulated industries, enterprise security communication is no longer optional — it is part of the core brand infrastructure.
Key challenges companies face
Misalignment between security and marketing teams
One of the most persistent issues is organizational silos. Security teams focus on risk mitigation and technical depth, while marketing teams prioritize clarity and audience engagement.
PwC reports that only 39% of executives say their cyber and business teams are fully aligned on risk priorities. This gap often results in content that is either overly technical or overly simplified, neither of which supports enterprise buyers effectively.
Difficulty translating technical risk into business value
Enterprise buyers — especially CFOs, procurement leaders, and boards — evaluate cybersecurity in financial and operational terms.
However, many organizations still publish content dominated by:
- Tool-centric messaging
- Feature comparisons
- Generic threat summaries
Without business framing, the content fails to influence high-level stakeholders. This is particularly problematic in complex B2B cybersecurity marketing strategy initiatives where multiple decision-makers are involved.
Compliance-driven messaging that lacks differentiation
Regulated industries such as financial services, healthcare, and energy often default to compliance-heavy communication. While necessary, compliance language alone rarely builds trust leadership.
According to Deloitte research, more than half of organizations struggle to communicate cyber risk in a way that resonates with business stakeholders. As a result, security messaging becomes standardized and indistinguishable across competitors.
Limited measurement of content effectiveness
Many enterprise teams still evaluate cybersecurity content using traditional marketing metrics such as page views or downloads.
While useful, these metrics rarely capture enterprise impact, such as:
- Influence on deal velocity
- Support for vendor risk assessments
- Contribution to RFP success rates
Without advanced measurement models, cybersecurity reporting content remains undervalued internally.
Best practices and professional approaches
Align cybersecurity messaging with enterprise risk frameworks
Mature organizations map their cybersecurity marketing strategy directly to recognized frameworks such as:
- NIST Cybersecurity Framework
- ISO/IEC 27001
- SOC 2 reporting
This alignment improves credibility with enterprise buyers. In practice, we often see that organizations adopting framework-aligned messaging experience shorter security review cycles, particularly in regulated procurement environments.
Build executive-ready security narratives
Effective IT security thought leadership translates technical posture into business language. High-performing teams typically structure their messaging around:
- Financial risk exposure
- Operational resilience
- Regulatory readiness
- Customer trust impact
Enterprises that adopt executive-focused narratives often report improved engagement from non-technical stakeholders during complex buying cycles.
Integrate security content into the full enterprise journey
Cybersecurity content should not live only in white papers or technical blogs. Mature enterprises embed security messaging across:
- Investor communications
- ESG and risk reports
- Product documentation
- Sales enablement materials
According to Forrester, organizations that integrate security messaging across the customer lifecycle can improve enterprise deal confidence by up to 20% in high-trust industries.
Establish measurable governance for security content
Leading teams treat cybersecurity content as governed enterprise assets. This typically includes:
- Quarterly content audits
- Cross-functional review workflows
- Version control and approval tracking
- Defined KPIs tied to pipeline influence
This governance model reduces inconsistency and supports scalable enterprise security communication.
Data, reporting, and documentation perspective
From a reporting standpoint, cybersecurity content marketing for B2B performs best when it is tightly connected to structured data flows.
In large enterprises, we typically see three reporting layers:
Operational dashboards
Security teams track incident response times, vulnerability closure rates, and threat detection metrics. These dashboards often update weekly or monthly.
Executive risk reporting
Boards and executive committees usually review cyber risk posture on a quarterly cadence. Metrics commonly include:
- Mean time to detect (MTTD)
- Mean time to respond (MTTR)
- Third-party risk exposure
- Compliance coverage
External trust communication
This includes customer-facing security pages, trust centers, and cybersecurity reporting content used in procurement.
Table: Common enterprise cybersecurity communication metrics
| Metric | Typical Enterprise Range | Primary Stakeholders | Source |
|---|---|---|---|
| Mean Time to Detect (MTTD) | 24–200 days | CISO, SOC leaders | IBM Security |
| Mean Time to Respond (MTTR) | 30–70 days | Incident response teams | IBM Security |
| Security review in B2B deals | 2–6 weeks | Procurement, legal | Gartner |
| Organizations increasing cyber budgets | ~65% | CIO, board | PwC |
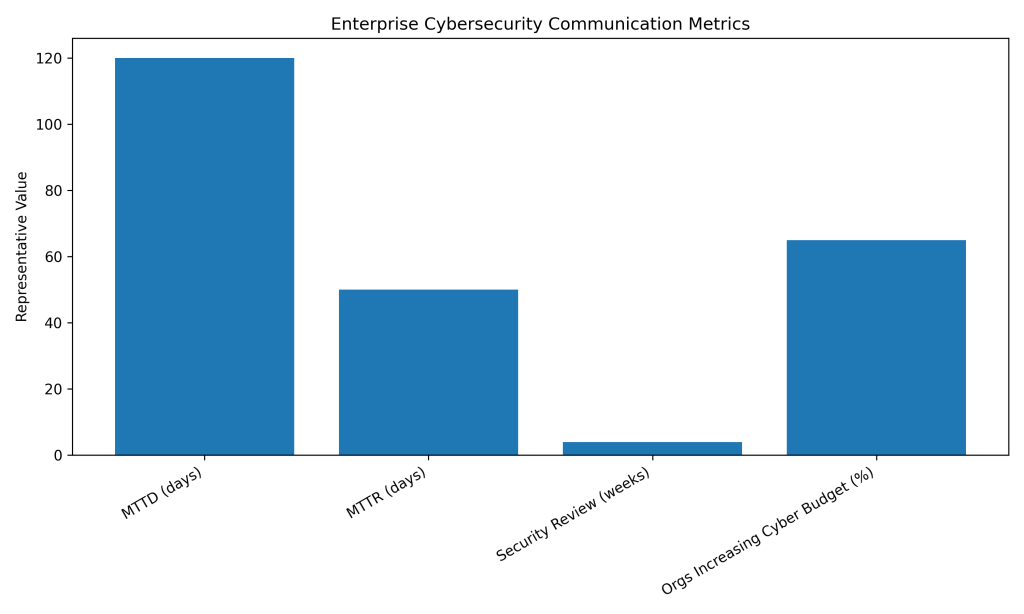
Table source references: IBM Cost of a Data Breach Report; PwC Global Digital Trust Insights; Gartner research.
These metrics highlight why structured cybersecurity marketing strategy efforts must be supported by credible data pipelines and governance discipline.
Common mistakes to avoid
Treating cybersecurity content as purely technical
When content is written only for engineers, enterprises risk losing executive engagement. This often results in longer sales cycles and repeated security questionnaires during procurement.
Over-relying on compliance language
Compliance statements are necessary but insufficient. Organizations that rely solely on certifications often struggle to differentiate in competitive enterprise markets.
Publishing without cross-functional review
Unreviewed security content can introduce legal and reputational risk. In some enterprises, inconsistent claims have led to extended vendor risk assessments and delayed deals.
Ignoring lifecycle integration
Security messaging that appears only during late-stage procurement forces sales teams into reactive mode. Enterprises that fail to integrate security earlier in the journey often experience longer deal cycles and higher pre-sales workload.
Using vanity metrics to measure success
Focusing only on downloads or impressions can mislead leadership. Without tying cybersecurity reporting content to pipeline or risk outcomes, organizations may underinvest in high-impact initiatives.
Conclusion
For large organizations navigating complex risk environments, cybersecurity content marketing for B2B is now a strategic discipline rather than a supporting tactic. It connects technical credibility with executive trust, procurement readiness, and long-term brand resilience.
Enterprises that align messaging with risk frameworks, governance processes, and measurable KPIs consistently outperform peers in high-stakes buying environments. With data breach costs averaging $4.45 million globally, the business case for structured, data-driven cybersecurity communication is stronger than ever.
In the years ahead, organizations that treat cybersecurity content as governed enterprise infrastructure — not just marketing output — will be best positioned to build durable trust in increasingly risk-sensitive markets.
References
- IBM Security. Cost of a Data Breach Report. https://www.ibm.com/reports/data-breach
- PwC. Global Digital Trust Insights. https://www.pwc.com/gx/en/issues/cybersecurity/global-digital-trust-insights.html
- Gartner. Forecast Analysis: Information Security and Risk Management Spending.
- Deloitte. Cyber Risk and Business Alignment Research.

